Some IoT Pentesting hints -- keep on update
A. Collect the information about the device
i.data sheets
ii.product features
iii.installation guide and user manual download from the vendor
website or use google dorks to get the data
B. as per device name and model number or hardware information check for publicly available exploits -exploit db , or exploit search engines useful search engines for the exploits
https://sploitus.com/
https://vulmon.com/
http://www.exploitsearch.com/
https://www.nmmapper.com/searchindex/s/
There are special search engines for IoT which helps us to find the more insecure devices which is publicly available
i. shodan
ii. censys
iii.zoomeye
iv. onphye
C. Making a detailed list
i. Write all features list of the device
ii. Make list publicly available exploits
iii.Start making your own method to pentest it -
before that understand device more clearly
D. Common approach for the IoT Pentesting Methodology
i.Network
ii.embedded applications
iii.mobile apps Android and ios
iv.wireless communications
v.firmware reversing
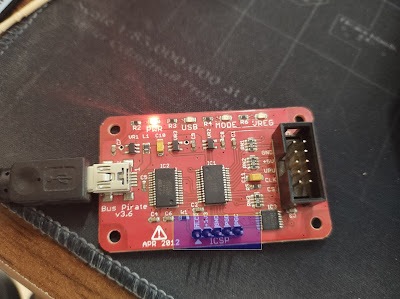
vi.hardware exploitation
vii.Side channel attacks
viii. radio communication attacks
ii. Make list publicly available exploits
iii.Start making your own method to pentest it -
before that understand device more clearly
D. Common approach for the IoT Pentesting Methodology
i.Network
ii.embedded applications
iii.mobile apps Android and ios
iv.wireless communications
v.firmware reversing
vi.hardware exploitation
vii.Side channel attacks
viii. radio communication attacks
A little more information
I.Network:
There is a much difference between the network pentesting in the IoT World until new protocol is added.
1. scan for the open ports and services version
2. easy one we can search for the already available as per the running services version
3. internal connected device connected to any other network outside use "netstat -antp" but we need a telnet access for this
4. FTP anon is a common bug in many IoT devices
5. search in firmware any network service related binary or script which help us lead the find a bug
6. debug the all network services (from extracted firmware)
II. Embedded Applications:
1. Do not think SQL injection until we got to know that device is communicating to a db with help of SQL
2. Most we need to look for the Command Injection and RCE
3. XSS(Stored high chances) Input locations always there to configure some of the settings which saves data
4. Mostly hardening is the solutions to fix the broken security configurations like authentication and authorization
5. Bruteforce on auth pages
6. Finding the parameters and access them without auth directly
7. Surely we will get more logical bugs than the technical bugs
8. all depends web technologies what they use
9. CSRF can always possible to depends on the Options enabled and account creation or settings pages
10. Webservices CoAP, REST Api
and MQTTweb configurations for auth issues encrypted communication
10. Useful tools
i. Burpsuite ( with plugins) & ZAP Proxy
ii. Wireshark
iii. Postman
III.Mobile APPS android and iOS:
For Android:
i. use dex2jar to convert the apk to jar file a
2. manually check for the data and look for write data service working exposure
3. check for the data is going to communicate with the device encrypted way or not
Usefultools
1. MobSF - Static analysis
2. Frida , burpsuite, apktool, dex2jar
3. OS- android tamer or Moblexer or IoT-PT
For iOS:
(will write soon)
IV.Wireless Communications:
1. Wireless communications - WiFi (ClientSide), ZigBee, Zwave, Bluetooth,LoRA
WiFi(Wireless Fidility):
V.Firmware Reversing:
1. basic checks for hardcoded credentials and private certificates
2. services exploits - running services binaries - like (ipv4, telnetd, ssh services , FTPD, encrypted binaries , authentication related binaries , decryption related binary/scripts
and search for more services and features and config files
3. check for syslinks will give an idea for the working way or services saving files one folder saving or communication will update here
4. Tools which helps you:
1. binwalk - extractor and many more
2. FACT tool - static analysis
3. Firmware Mod Kit
4. Fwanalyzer
5. Qemu - dynamic analysis
6. Qiling - for dynamic analysis
7. FAT - Firmware analysis tool


Comments
Post a Comment