Bluetooth Pentesting guide 101
Just interesting in daily life that we cant see properly called signals that we can't see with our own eyes
but devices can do there many wireless communication are there like
Well same procedure what we scan the surrounding devices and start attacks from the write-ups available in google
Let’s see little difference right now we need to know how Bluetooth works




but devices can do there many wireless communication are there like
Wireless Communication protocols in IoT:
- wifi (wireless fidelity)
- bluetooth
- zigbee
- zwave
- LoRA
- GSM
But let's get into the topic Mostly relevant
Vulnerabilities in Bluetooth:
- Authentication and authorization issues
- MiTM
- DoS
- MAC Spoofing
- PIN Cracking
- Brute force
In android Bluetooth mostly we will get this type vulnerability:
- RCE Remote code Execution
- EoP Elevation of Privilege
- ID Information Disclosure
- DoS Denial of Service
- PAIR Pairing without Auth
In major level:
- Hardware
- Memory Leakage
Well same procedure what we scan the surrounding devices and start attacks from the write-ups available in google
Let’s see little difference right now we need to know how Bluetooth works
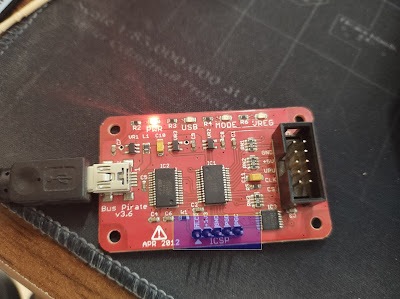
Lets start with Required installation tools:
A written bash script for the BLE Pentesting tools to install in a Ubuntu or debian OS
just download from here
wget https://raw.githubusercontent.com/IoTSecurity101/BLE-UAE/master/ble_uae.sh
And give the permission to run chmod +x ble_uae.sh
#./ble_uae.sh
Will install requirement tools with dependencies as well.All good with tools what i need to do just need to understand what to do before we need to start hacking , fuzzing and MiTM on BLE devices
ESP32 - Espressif Device
Smartband bought from flipkart - 359 /- Rupees - or we can buy from the banggood or any other online sellers
Bluetooth Pentest Guide:
---------------------------------
1. Flashing the codes to ESP32
2. Understanding BLE with Mobile App Configuration
3. Recon Techniques
4. Finding the Vulnerabilities
5. Python & easy bash scripts
6. Cheatsheet
General Cheat Sheet
dmesg | egrep -i 'blue|firm'
Hcitool tool:
hciconfig - sudo apt-get install bluez
For Non LE Devices:
hcitool scan - to scan the basic bluetooth devices
hcitool info <baddr> -
For LE Devices :
hcitool lescan - for scanning the LE devices
hcitool leinfo <baddr> - for getting the info of the LE Devices
Install bleak
sudo pip3 install bleak
sudo pip install service_identity
Usage : sudo bleak-lescan
SDPTOOL :
sudo sdptool browse --tree --raw <baddr> : Browse all available services on the device specified by a Bluetooth address as a parameter



Comments
Post a Comment