OWASP IoT I9: Firmware analysis part -1
Firmware static analysis is a process used to examine the firmware of IoT devices and other embedded systems without executing the code. This analysis is crucial for identifying vulnerabilities, security flaws, or violations of coding standards, misconfiguration and hardcoded data within the firmware.
The general what i follow after dumping firmware from hardware.
• Get the
firmware (vendor/hidden forums/dumping from hardware)
•
Reconnaissance (get to know about architecture and filesysteminfo)
•
Unpacking (extracting firmware also fun)
•
Localize point of interest (always keep the priority what exactly looking for (hardcoded data, or shell scripts or command injetion function))
•
Decompile/pentest/fun! (binary decompiling)
What are the requirements i will explain step by
step. Here i am using the Ubuntu Xenial 16.04 you can use which Linux is
comfortable with you.
Static analysis tools:
| Name | Description |
|---|---|
| EMBA (Embedded Malware Binary Analysis) | A Python-based framework for analyzing and reversing embedded malware found in firmware and bootloaders. It supports various architectures, including ARM, MIPS, and x86. EMBA provides a range of tools for static and dynamic analysis, including disassembly, debugging, and emulation. |
| FACT (Firmware Analysis and Comprehension Tool) | A tool for static analysis of firmware images, including disassembly, decompilation, and symbolic execution. FACT supports various file formats, including ELF, SREC, and HEX. It provides a graphical user interface (GUI) for visualizing the disassembly output and a scripting interface for automating analysis tasks. |
| Objdump | A tool for disassembling binary files into assembly code. Objdump supports various file formats, including ELF, COFF, and PE. It provides a range of options for controlling the output format and disassembly options, such as addressing modes and instruction mnemonics. |
| Binwalk | A tool for binary analysis, including the detection of file formats, compression algorithms, and encryption schemes. Binwalk supports various file formats, including ELF, PE, and ISO images. It provides a range of options for controlling the analysis process, such as verbosity level and output format. |
| Unblob | A tool for unpacking compressed binaries, including UPX, PECompact, and UPack. Unblob supports various file formats and compression algorithms. It provides a range of options for controlling the unpacking process, such as output format and passwords. |
| Firmwalker_pro | A tool for firmware analysis, including the detection of firmware images, the extraction of metadata, and the identification of known vulnerabilities. Firmwalker_pro supports various file formats and architectures. It provides a range of options for controlling the analysis process, such as verbosity level and output format. |
| binbloom | A tool for binary similarity detection, using Bloom filters to quickly identify similar binaries based on their hash values. Binbloom supports various hash algorithms and database formats. It provides a range of options for controlling the similarity search process, such as threshold values and output format. |
| bytesweep | A tool for binary pattern matching, using regular expressions to search for specific patterns within binary files. Bytesweep supports various file formats and regular expression dialects. It provides a range of options for controlling the pattern matching process, such as case sensitivity and output format. |
| fwanalyzer | A tool for firmware analysis, including the detection of firmware images, the extraction of metadata, and the identification of known vulnerabilities. Fwanalyzer supports various file formats and architectures. It provides a range of options for controlling the analysis process, such as verbosity level and output format. |
| firmware.re | A tool for firmware reverse engineering using Python’s re module to search for specific patterns within binary files and extract relevant information. Firmware.re supports various file formats and regular expression dialects. It provides a range of options for controlling the reverse engineering process, such as case sensitivity and output format. |
| checksec | A tool for binary security analysis, including the detection of stack canaries, NX (No eXecute) protection, and ASLR (Address Space Layout Randomization). Checksec supports various file formats and architectures. It provides a range of options for controlling the security analysis process, such as verbosity level and output format. |
| strings | A tool for extracting strings from binary files using heuristic algorithms to identify printable ASCII strings and null-terminated strings. Strings supports various file formats and encoding schemes. It provides a range of options for controlling the string extraction process, such as case sensitivity and output format. |
| hexdump | A tool for displaying binary data in hexadecimal format with optional formatting options such as byte offsets and byte widths |
So here i am not attacking any device directly
because for firmware you will get from the vendor site, or you can find some
firmware in index of some sites.
Installation:
1.Binwalk:
as shown below And follow the installation steps from the Github location some dependencies need to be install. Some of them i will show how to do and remaining check from here
https://github.com/ReFirmLabs/binwalk/blob/master/INSTALL.md
$sudo apt-get install binwalk
2.Strings:
After installation in the Binwalk in my Linux
operating OS so next strings already default many Linux systems if it’s not
there then install strings and Hexeditor
Strings using for printable characters in files. Depending upon
how the strings program was configured it will default to either displaying all
the printable sequences that it can find in each file, or only those sequences that are in
loadable, initialised data sections. If the file type in unrecognisable, or if
strings is reading from "stdin" then it will always display all of the printable
sequences that it can find.
3.hexedit tool:
hexedit tool - view and edit files in hexadecimal or in
ASCII.
4.Linux OS:
Here coming for the firmware analysis many Linux OS
having some problems while doing the testing, so i am choosing Ubuntu
You can choose other Linux as well but issues found many
5. Vulnerable Firmware:
In firmware testing we required a firmware and why i
mentioned vulnerable firmware here , i am not going to target any particular
device , the people who are working in this firmware analysis they designed one DVRF - Damn Vulnerable Framework Router , we
are going test DVRF you can
download from here:
Some other firmware files to test
Here i am showing the a simple firmware of “openwrt” for testing purpose you can
download with help of Google dorks also for example: “index of firmware”
Before going to start the "firmware analysis"
What is firmware:
Firmware is a software for hardware, and it is helped
for the user running programs on the devices
Where it is available :
1. CD/DVD from vendor
2. Device Vendor websites
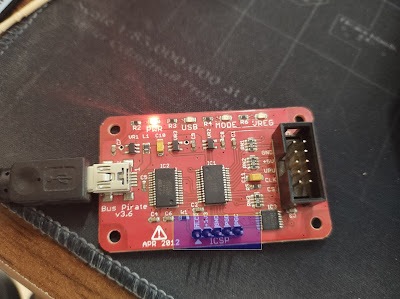
3. Dump with the help of hardware debuggers from the
devices.
4. Capture when updating firmware
5. Reversing APPS
What is firmware testing:
Firmware testing is nothing but finding the bug
inside of firmware before hackers do ..
In firmware testing main flaw findings are buffer/stack/heap over flows , so some other testing are like functionality test and security
test , so we are discuss about the security test.
Why firmware testing:
Firmware is consist of hidden data and it is
controller of device which means once find the vulnerabilities like are zero days in
firmware , that firmware related all devices can be hackable , already many
hacks exposed like “netusb” related hacking techniques , so before hackers taking
advantage of devices hacking will go for test first,
Lets get into testing:
Before i am going to test i want to say something to
all, this is not only final or advanced method, as a beginner it will give
some idea on testing, there many more methods are there i am keep writing for
the different types of testing of firmware analysis and IoT hacking also.
1. File
information
2. Printable
characters analysis
3. Identify
the Build of firmware.
4. Reverse
engineering with the Binwalk.
5. Finding
the confidential information
Run “file” command in on testing binary file to get the data
information of bin file,
A data contains of the .txt files and .bin files, when
we are running the file command it will showing the data it means bin file
containing information.
# file “file.bin”
And check for the printable characters in bin file
with help of “strings.”
# strings -n 10 “file.bin”
The above image is giving the information of the architecture of “MIPS”there are two main types of architecture MIPS and ARM,
MIPS(Million Instructions Per Second):
This architecture is mainly in Routers and Play stations, and it is is a reduced instruction set computer (RISC)ARM(Advanced RISC Machine):
this architecture is using for the mainly mobiles,
and SoC
(system on chips), radios etc.
Identify the Build of firmware:
For finding the firmware build information we are
going to use Hexdump
# hexdump -C -n 512 xyz.bin
Analysis with Binwalk:
With help of binwalk we can find more information from
the firmware files so let's begin
Here we go for the testing firmware file.
Here we going to check for the signatures and file
containing inside of binary file]
$binwalk “file.bin”
After that what we got information about the given file containing,
LZMA compressed data, squashfs file system, and some
other information for video actually what are they.
The Lempel–Ziv–Markov chain algorithm (LZMA) is an algorithm used to perform lossless data compression.
SquashFS is a compressed read-only file system for Linux. SquashFS compresses files, inodes and directories, and supports block sizes up to 1 MB for greater compression.
And it is containing information of passwords, certificates, running services, architecture information, Api's, firmware upgrade URL's and many other sensitive information that we need to check manually or automated way.
Extracting the data form the firmware and analyzing the information what it contains.
$binwalk -Me “file.bin”
In binwalk “M” for even recursively scan files as it extracts them, for extracting firmware we choose option “e” after extracting looking like this as shown below.
And like that grab the banner information and root information
Command:
$cat etc/banner
For finding the Confidential information form the extracted files
Some interesting information is available like passwords, root information and certificated, hardcoded URL’s etc.
Once squashfs folder is extracted we will get more information from it like passwords,
Go to extracted folder as shown below.
$cat /etc/passwd$cat /etc/shadow
To check additional information about
Firmware like release and version information















Comments
Post a Comment